Your cart is currently empty!
threats
-
Hide anything in everything
or, ‘when you try to see everything, you will miss something’ There is no way There is no way to monitor everything. Intrinsically, everybody knows this. However, the promise of a Panopticon still intrigues many a manager or policy maker in security. This means every now and then (and in the last few years it was mostly the…
-

Hack and Leak Crime
Hack and leak crimes are on the rise, and from what I’ve seen in cybersecurity, they can devastate businesses, individuals, and governments. These attacks are as simple as they are dangerous. A hacker breaches a system, steals sensitive data, and releases it publicly, often causing long-lasting damage. The impact can ruin reputations, cripple organizations, and…
-

Supply Chain Attacks: Why Your Vendors Could Be Your Biggest Risk
Supply chain attacks target the weakest link in your ecosystem, and once an attacker compromises a supplier, they can worm their way into your organization. I’ve been in the cybersecurity space long enough to know one thing: the biggest threat often doesn’t come from within your own network. It’s your trusted partners, vendors, and suppliers…
-
The Cyber Threat Intelligence Capability Maturity Model (CTI-CMM)
In the ever-evolving landscape of cyber threats, organizations need a solid framework to assess and enhance their cyber threat intelligence (CTI) capabilities. Enter the Cyber Threat Intelligence Capability Maturity Model (CTI-CMM), a powerful tool designed to help organizations evaluate their current CTI practices, set ambitious goals for improvement, and benchmark their performance against industry standards.…
-

Top 10 Dark Web Forums Dominating Cybercrime
The dark web hides countless forums, unseen by conventional internet users. These forums serve as hotspots for cybercriminals, dealing in stolen data, hacking tools, and illicit services. Let’s explore these digital underworlds, each one playing a crucial role in the cybercrime ecosystem. An Overview of Cybercrime Forums 1. BreachForums BreachForums gained prominence after RaidForums shut…
-
CVE-2024-38396: A Critical Vulnerability in iTerm2
This vulnerability, found in iTerm2, a popular terminal emulator for macOS, can have serious implications if exploited. What is CVE-2024-38396? CVE-2024-38396 is a security flaw discovered in iTerm2 versions 3.5.x before 3.5.2. This issue1 involves the unfiltered use of an escape sequence to report a window title. When combined with the built-in tmux integration feature,…
-
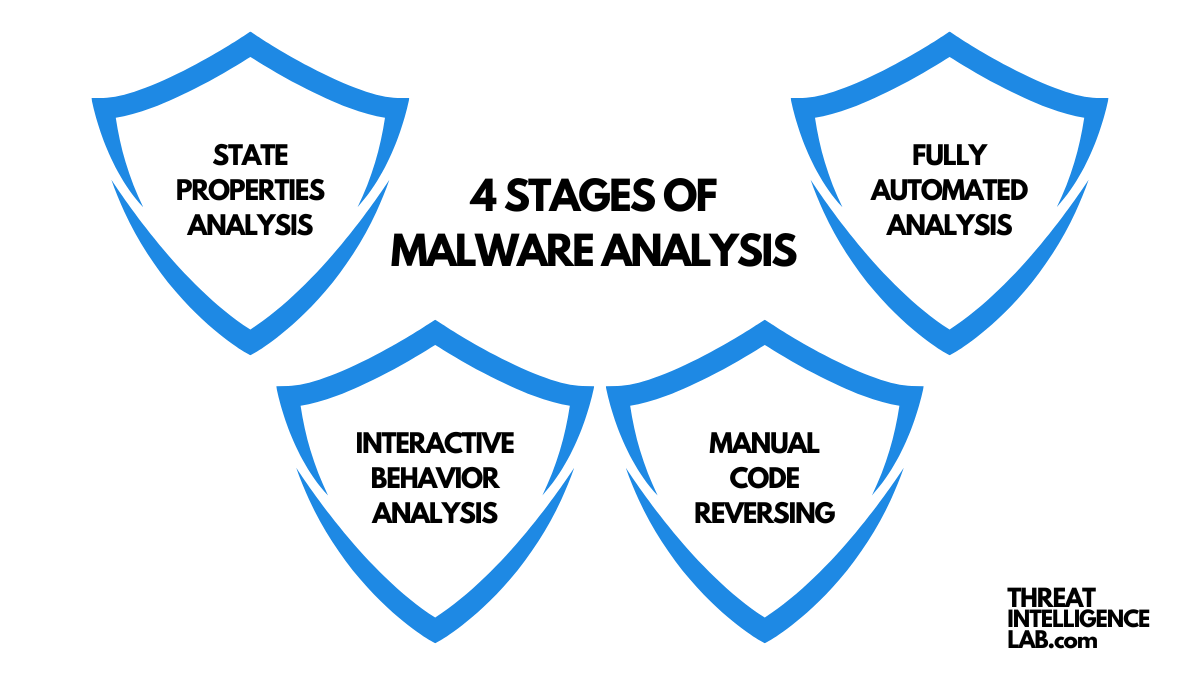
What is Malware Analysis?
Malware analysis is all about understanding how malware works, the different types it comes in, how it’s used in real situations, and the tools needed to investigate and analyze it thoroughly. It helps uncover the behavior, purpose, and potential impact of malicious software. This guide will walk you through the key aspects of malware analysis,…
-

Why Cybercriminals Chase Your Personal Information
When we talk about data security, the term “Personal Identifiable Information” or PII often comes up. I’m here to explain what PII is and why it’s a hot target for cybercriminals. What is Personal Identifiable Information (PII)? PII is any information that can identify a specific individual. It includes various types of data that, alone…
-
Software Supply Chain Attacks: Insights and Defense Strategies
I often encounter questions about software supply chain attacks. These attacks can devastate organizations, especially as our reliance on third-party software components grows. Knowing how to identify and mitigate these threats is critical. Let’s explore what software supply chain attacks are, their impact, and effective defense strategies. What Are Software Supply Chain Attacks? Software supply…
-

Understanding Threat Intelligence Platforms (TIPs)
In the world of cyber threat intelligence, one tool stands out: the Threat Intelligence Platform (TIP). As someone with years of experience in cybersecurity and threat intelligence, I can say that TIPs are essential. But what exactly are TIPs, and why are they so crucial? Ill try to explain this. What is a Threat Intelligence…